COMPANY
About Us
Our Story
Most security products and approaches start with some version of “first, centralize all your security data.” SYSLOG, SIM, SIEM, Data-lakes, Cloud SIEM, XDR — this is not even a complete list. Many companies are centralizing partial data in five or more places.
It’s not uncommon for the same security data to transit one cloud provider more than three times, as it is processed by different security tools and then stored in multiple places. The centralization itself takes much time and effort but worse yet, there is a critical loss of fidelity — truncated data, lack of real-time, lack of contextual links, and forced prioritization of centralized data sources.
Cloud and SaaS adoption continue to rise, and security relevant data is growing tremendously. Even if you have an unlimited budget (please reach out if you do!), it’s not practical or effective to centralize all the data your security team might find useful.
We can’t end all centralization of security data. But we are focused on getting better answers from your security data – wherever it lives, with a single search plus the context for you to understand what action to take next. We want to take the friction out — from knowing where data resides, how to access it, how to search it, and how to enrich it — so you can take action.
When you are investigating a potential security issue, hunting for a specific adversary, or any of dozens of other security operations practices, you need fast answers to your questions, with the context to inform what to do next. We plan to flip the balance of time spent moving data, accessing data, triaging data, and learning all that goes with how to search it, to actually getting the answer to the question you seek.
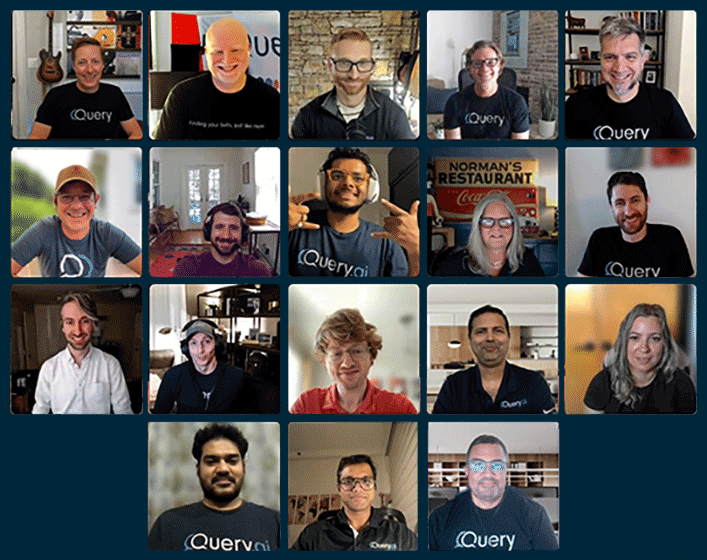
The team at Query has been working in security operations since what feels like the dawn of (Internet) time. We are here to enable security teams to get answers to important search questions without centralizing more data. We are starting with common threat cases that require cloud and SaaS data that are probably not in your super cool central logging repository today.
And that’s just the beginning. There are valid reasons to centralize and store data, and often centralization happens in multiple places. Wherever your data is (leave it there), it should not limit your ability to get answers to the questions you seek when you need them. We are always building out new data integrations, threat cases, and ways to help operators understand security data. Join us, and let’s change how we search for the security answers we need when we need them most.